Security questionnaires are one of the most time-consuming parts of vendor risk management. Every time a company evaluates a new vendor or a vendor sells to a new enterprise customer, the same process repeats: long spreadsheets, hundreds of security questions, and weeks of back-and-forth clarification.
To reduce this friction, a growing number of organizations are turning to AI tools for security questionnaires. These tools promise to automatically generate responses, analyze vendor answers, and speed up third-party risk assessments.
While AI can significantly improve efficiency, many organizations are discovering that AI questionnaires alone don’t fully solve vendor risk management bottlenecks.
Understanding why requires looking at how vendor security assessments actually work.
Why security questionnaires exist
Security questionnaires are designed to help organizations evaluate whether a vendor’s security practices meet internal and regulatory requirements.
Typical questionnaires include questions about:
- Access control and identity management
- Encryption practices
- Data storage and retention
- Incident response procedures
- Compliance certifications such as SOC 2 or ISO 27001
These questionnaires are widely used because third-party vendors represent a significant security risk.
Industry research consistently shows that third-party vendors are involved in a large percentage of data breaches. For example, a Ponemon Institute study found that 51% of organizations experienced a data breach caused by a third party.
As companies adopt more SaaS tools and cloud services, vendor ecosystems grow rapidly. Many enterprises now manage hundreds of third-party vendors, each requiring some level of security evaluation.
Security questionnaires became the default method for performing this due diligence.
The growing burden of security questionnaires
While questionnaires help standardize vendor assessments, they also create operational challenges.
A typical enterprise security questionnaire may contain 200 to 400 questions, and large vendors often receive dozens of these requests from different customers every year.
This leads to several common problems:
Repeated work for vendors
Vendors frequently answer similar questions from multiple customers, often in slightly different formats.
Slow review cycles
Security teams must manually review responses, request clarification, and validate evidence.
Delayed vendor onboarding
Vendor risk assessments can delay product launches and partnerships because security approval takes weeks or months.
According to multiple TPRM industry reports, vendor risk assessments often take three to twelve weeks to complete, depending on vendor complexity and internal review processes.
This inefficiency is what drove the rise of AI tools for security questionnaires.
What AI tools for security questionnaires do
AI-powered tools aim to automate parts of the questionnaire workflow. Instead of manually answering or reviewing hundreds of questions, organizations can use AI to accelerate the process.
Most AI questionnaire tools focus on several key capabilities.
AI-Generated responses
For vendors, AI can automatically generate responses by analyzing existing materials, such as:
- Previous questionnaires
- Security policies
- Compliance reports
- Internal documentation
This allows vendors to complete questionnaires significantly faster.
Learn more about the VISO TRUST AI Agent
Knowledge base matching
AI systems can match incoming questions against an existing knowledge base of answers.
If a similar question has already been answered in the past, the system can suggest or automatically populate the response.
This reduces duplication and helps maintain consistency across responses.
Framework mapping
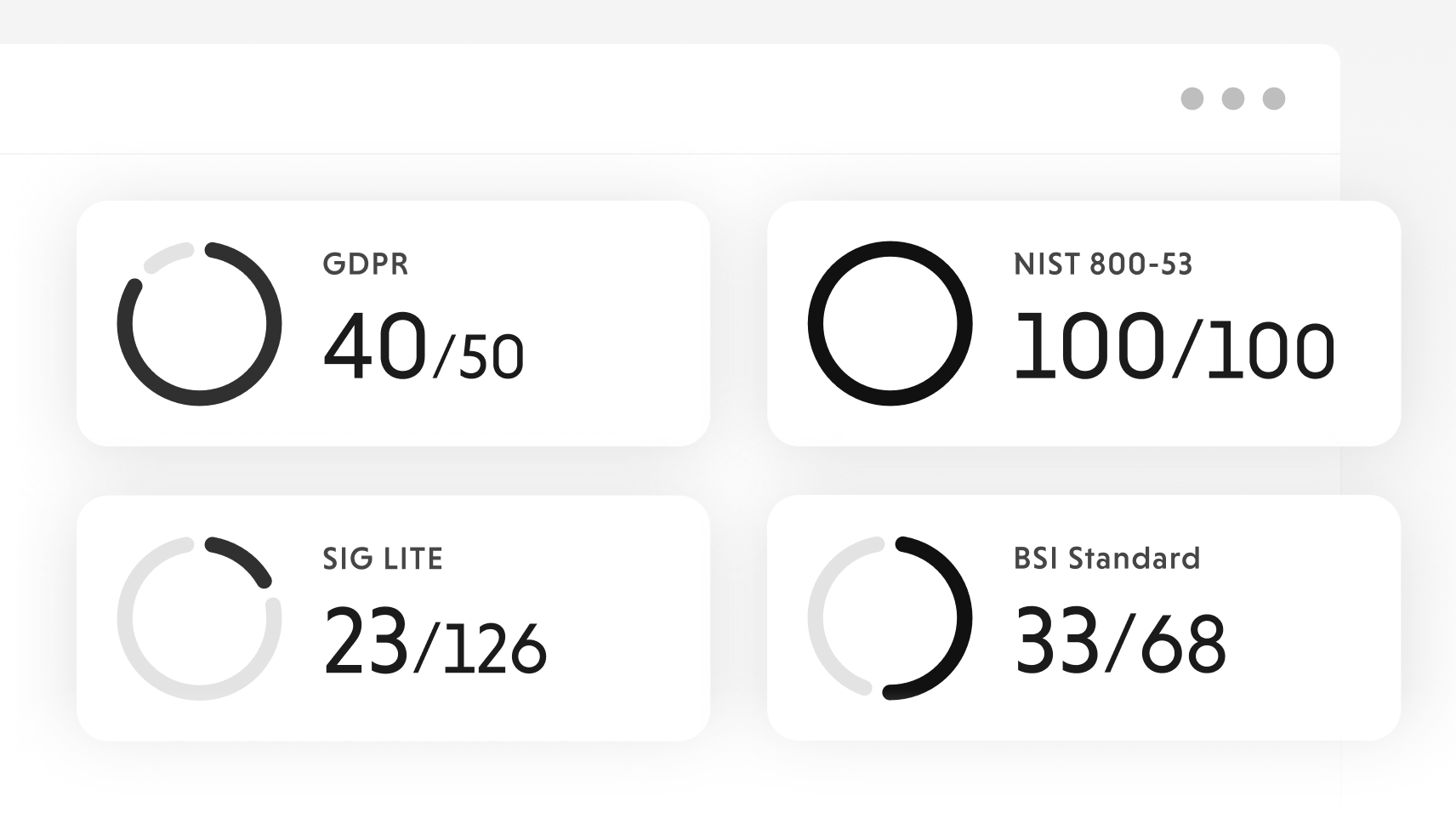
Many AI tools automatically map questionnaire responses to common security frameworks, such as:
This allows organizations to reuse answers across different questionnaires and compliance programs.
Response analysis
Security teams can also use AI to analyze vendor responses.
Some tools highlight:
- Missing answers
- Potential security gaps
- Inconsistent responses
- Areas requiring additional evidence
This can help reviewers focus on higher-risk issues rather than reading every question manually.
Why AI questionnaires still create bottlenecks
Although AI tools reduce manual effort, they do not fundamentally change the questionnaire process.
The workflow still depends on a static list of predefined questions.
This creates several limitations.
First, questionnaires assume that vendor risk can be evaluated through a fixed checklist.
In reality, risk assessments often require context-specific investigation.
For example, security teams may need to understand:
- The exact data a vendor processes
- How systems integrate with internal infrastructure
- Whether subprocessors are involved
- How AI features use customer data
These questions vary depending on the vendor’s product architecture and the organization’s risk tolerance.
A generic questionnaire cannot anticipate every scenario.
Real vendor risk investigations are dynamic
In practice, security teams rarely rely solely on questionnaires.
During vendor assessments, they frequently ask follow-up questions such as:
- “Does this integration store or only process customer data?”
- “Which cloud provider hosts this service?”
- “Can you provide encryption documentation for this specific feature?”
- “Does the vendor’s AI system train on customer data?”
These types of questions are contextual and evolving.
They arise during the investigation process, not in the original questionnaire.
As a result, security teams still spend significant time asking additional questions, requesting documentation, and verifying evidence.
This is why many vendor risk programs still experience delays even after adopting AI questionnaire tools.
The emerging shift beyond questionnaires
To address these limitations, the next generation of vendor risk technology is beginning to move beyond questionnaires entirely.
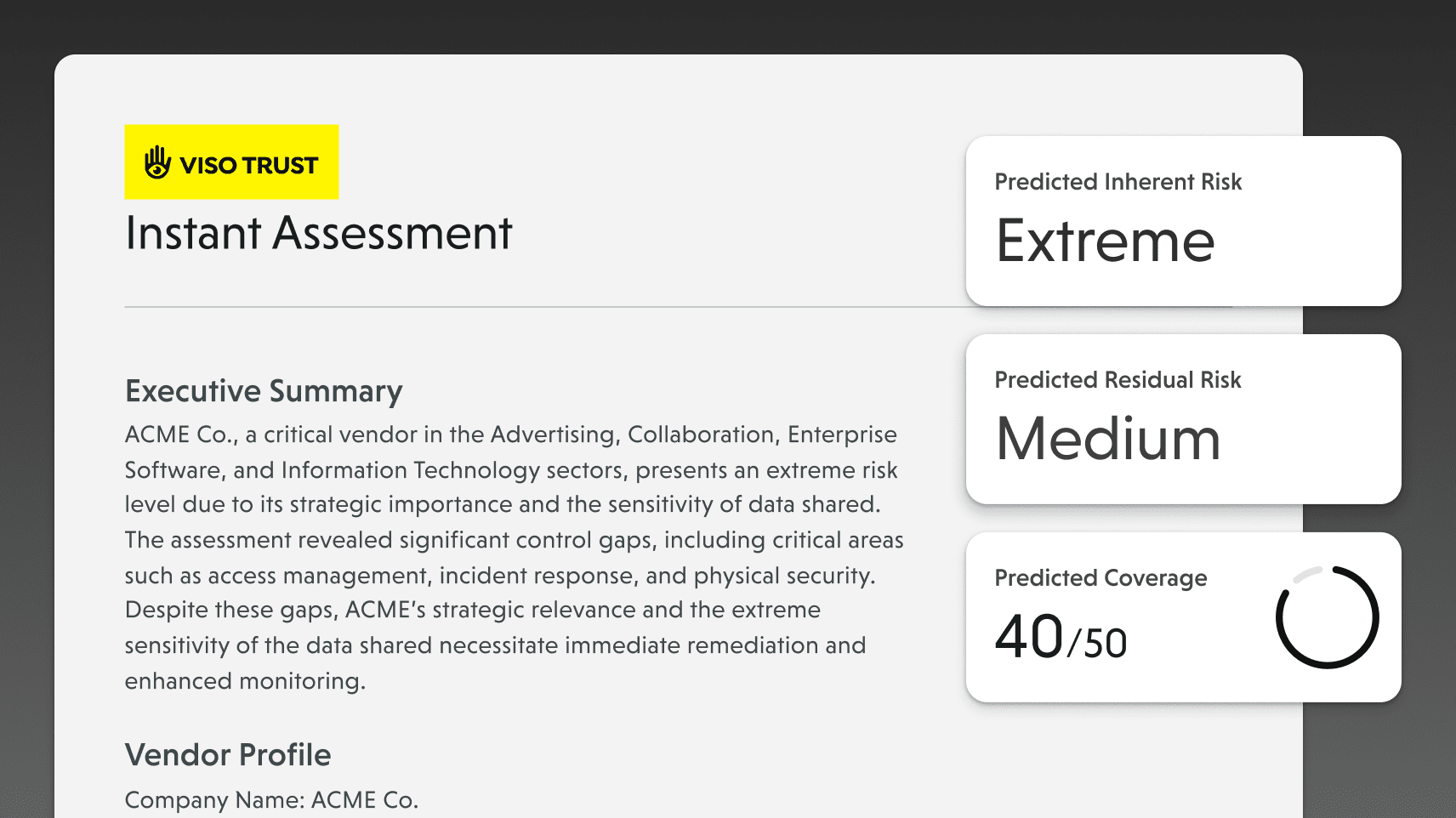
Instead of simply automating questions, newer systems focus on automating the evidence-gathering process.
This approach includes several capabilities.
Automated evidence collection

Rather than asking vendors to manually answer questions, systems gather information directly from available sources such as:
- SOC 2 reports
- Compliance certifications
- Vendor trust portals
- Public security documentation
This reduces the number of questions that need to be asked in the first place.
Targeted vendor requests
When additional information is needed, systems generate specific evidence requests rather than sending long questionnaires.
For example:
Instead of asking dozens of encryption questions, a system may request documentation showing how a specific data store is encrypted.
This allows security teams to focus on verifying evidence rather than reviewing checklists.
Continuous vendor monitoring
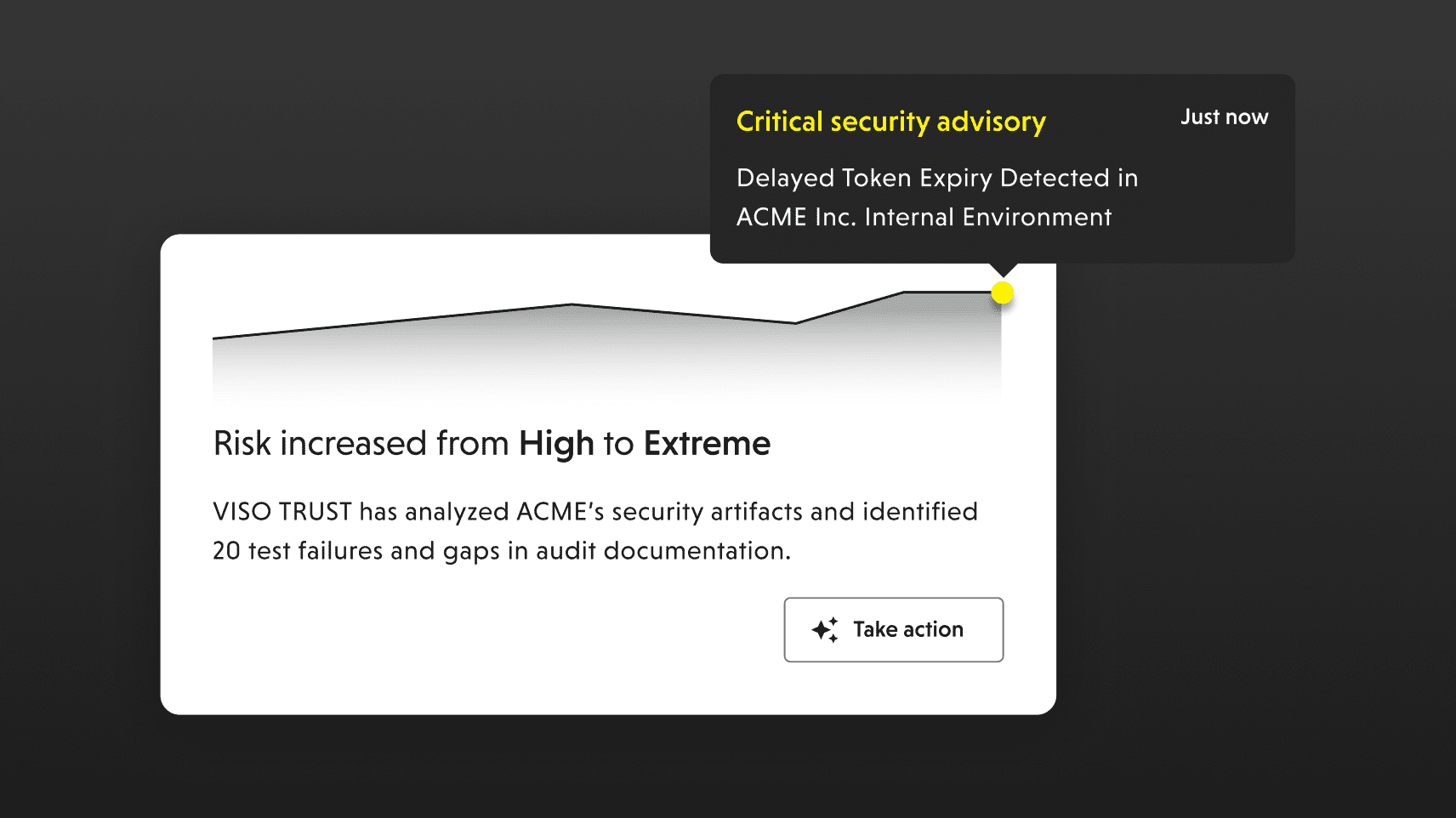
Traditional questionnaires happen once during onboarding or annual reviews.
However, vendor security posture can change at any time.
Modern vendor risk platforms increasingly monitor vendors continuously for:
- New vulnerabilities
- Security incidents
- Compliance updates
- Infrastructure changes
This provides ongoing visibility rather than relying on periodic questionnaires.
The future of AI tools for security questionnaires
Security questionnaires will likely remain part of vendor risk programs, but they will play a smaller role as automation improves.
The next generation of tools focuses on automated investigation, evidence validation, and continuous monitoring of vendor ecosystems. These capabilities are increasingly being delivered through AI TPRM platforms designed specifically to eliminate manual vendor risk workflows.
As vendor ecosystems grow and technology stacks become more complex, organizations need smarter ways to evaluate risk.
Organizations evaluating new tools should also review the best AI vendor security assessment software solutions to understand how different platforms approach automation, AI-driven analysis, and third-party risk monitoring.
The future of vendor risk management will likely combine:
- Automated evidence collection
- Context-aware risk analysis
- Continuous vendor monitoring
- AI agents that investigate vendor security posture
In other words, the goal is not simply faster questionnaires. The goal is to ask fewer, but more meaningful questions.