Top Whistic Competitors and Alternatives
2026 Comparison Guide
When security and procurement-focused teams evaluate third-party risk management (TPRM) platforms today, they’re looking for more than just questionnaires. They need an AI-powered risk management platform that delivers continuous visibility into security risk, automates vendor assessments, and scales without adding operational overhead.
In this guide, we compare leading Whistic alternatives:
- VISO TRUST
- Whistic
- UpGuard
- Vanta
- Safe Security
- CyberGRX
- Black Kite
We’ll break down where each solution fits and where enterprise programs often require more advanced capabilities.
Learn more about VISO TRUST’s TPRM software
Why organizations are looking for Whistic Alternatives
Whistic helped modernize vendor reviews by centralizing questionnaires and allowing vendors to publish shared profiles. For many teams, that was a major step up over email chains and PDFs.
But as vendor ecosystems expand, limitations appear:
- Risk reviews remain point-in-time
- Security teams still wait on vendors to respond to security questionnaires
- Reassessments require manual tracking
- Risk decisions lack real-time vendor intelligence
- Security posture changes between assessments
In today’s competitive landscape, enterprise programs require continuous monitoring, deeper risk assessment automation, and visibility into vendors based on real operational signals (not just static survey answers).
See more cybersecurity comparisons
What Modern Vendor Risk Management Requires
Before diving into a specific platform, it’s important to define what mature vendor risk management should include:
- AI-powered analysis of vendor documentation (SOC 2, ISO 27001, penetration tests)
- Automated assessment workflows
- Continuous monitoring of vendor security posture
- Measurable risk scores
- Real-time vendor alerts
- End-to-end TPRM workflow automation
- Scalable third-party risk management infrastructure
VISO TRUST

VISO TRUST is an AI-powered risk management platform purpose-built to modernize third-party risk management beyond questionnaire exchanges.
Unlike questionnaire-centric platforms, VISO TRUST automates vendor assessments by ingesting real vendor artifacts (SOC 2 reports, ISO 27001 certifications, policies, and technical documentation) and extracting actionable control insights.
What Makes VISO TRUST Different
- AI-driven document analysis replaces manual review
- Automated control mapping to security frameworks
- Continuous monitoring across the vendor lifecycle
- Real-time vendor alerts
- Risk scores based on evidence, not just surveys
- Full TPRM workflow automation from onboarding to offboarding
Instead of waiting around for vendors to respond to security questionnaires, security teams receive data-driven insights immediately.
Best fit: Enterprise security, procurement, and compliance teams managing complex vendor ecosystems who need scalable vendor risk management without the added headcount.
Whistic
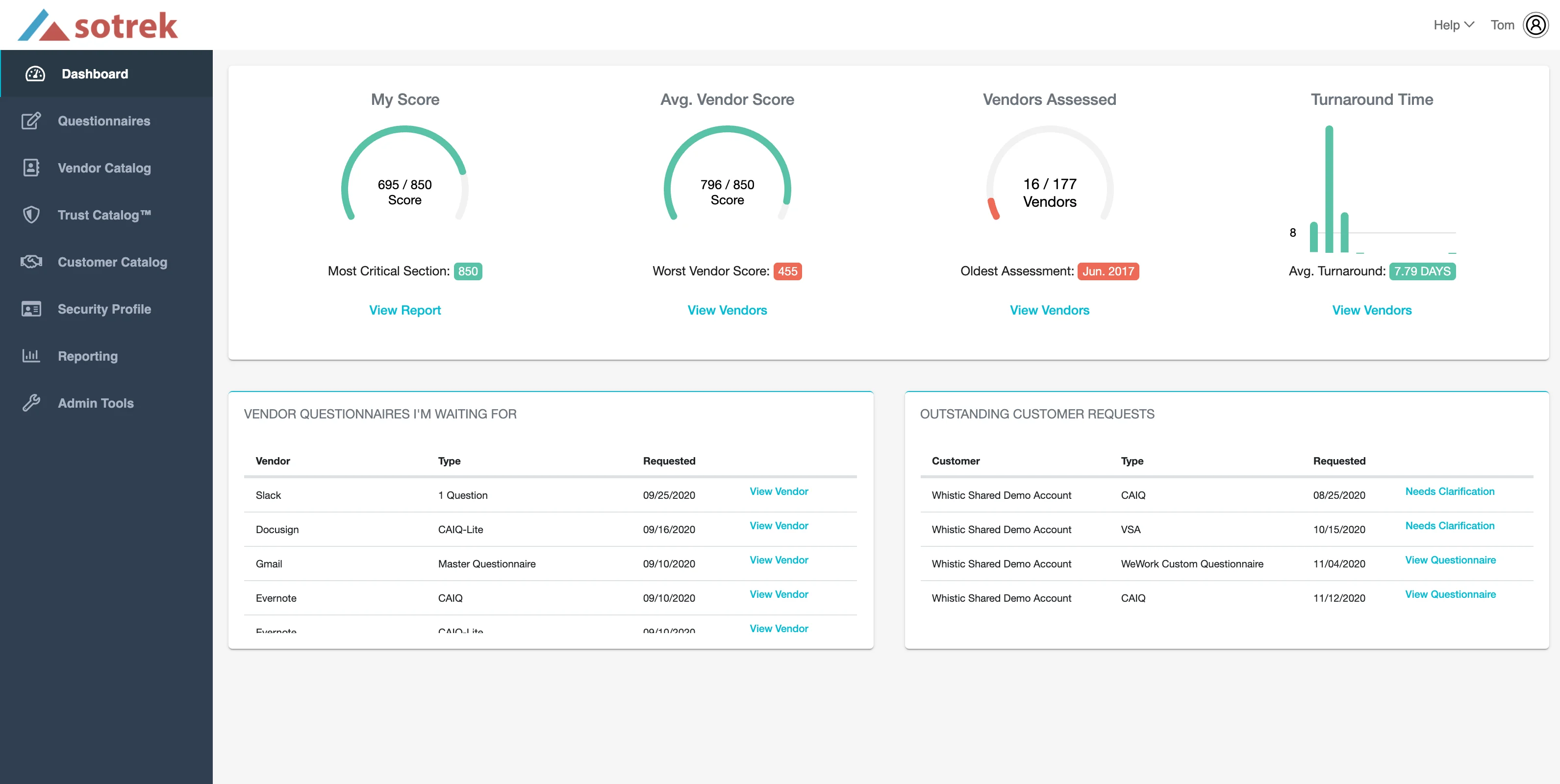
Whistic helps reduce duplication in vendor reviews by enabling vendors to publish shared profiles.
Strengths:
- Centralized security questionnaire management
- Vendor profile exchange to reduce repeated requests
- Structured assessment workflows
Limitations:
- Risk remains point-in-time
- Still dependent on vendors to respond to security questionnaires
- Limited continuous monitoring capabilities
- Security posture may change between assessment cycles
Whistic works well for teams transitioning from spreadsheets, but organizations seeking real-time vendor insights and AI-powered automation often explore alternatives.
See the Whistic vs TPRM alternatives
Upguard
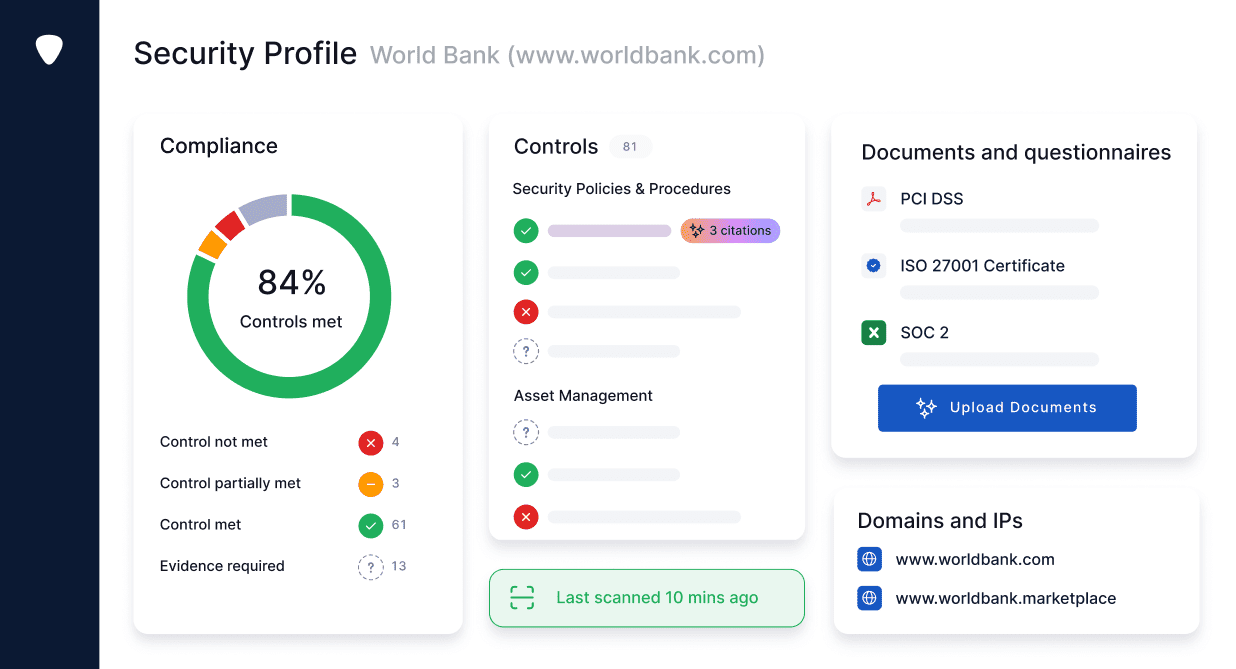
Upguard combines vendor risk management with external security posture monitoring.
Strengths:
- Continuous monitoring of external attack surfaces
- Risk scores from observable data
- Vendor comparison dashboards
Limitations
- Primarily outside-in risk visibility
- Limited deep evidence analysis from internal vendor documentation
- Assessment workflows still rely on questionnaires for control validation
Upguard is strong for monitoring external security posture, but does not fully replace comprehensive AI-driven vendor assessments.
Learn more about Upguard vs TPRM alternatives
Vanta
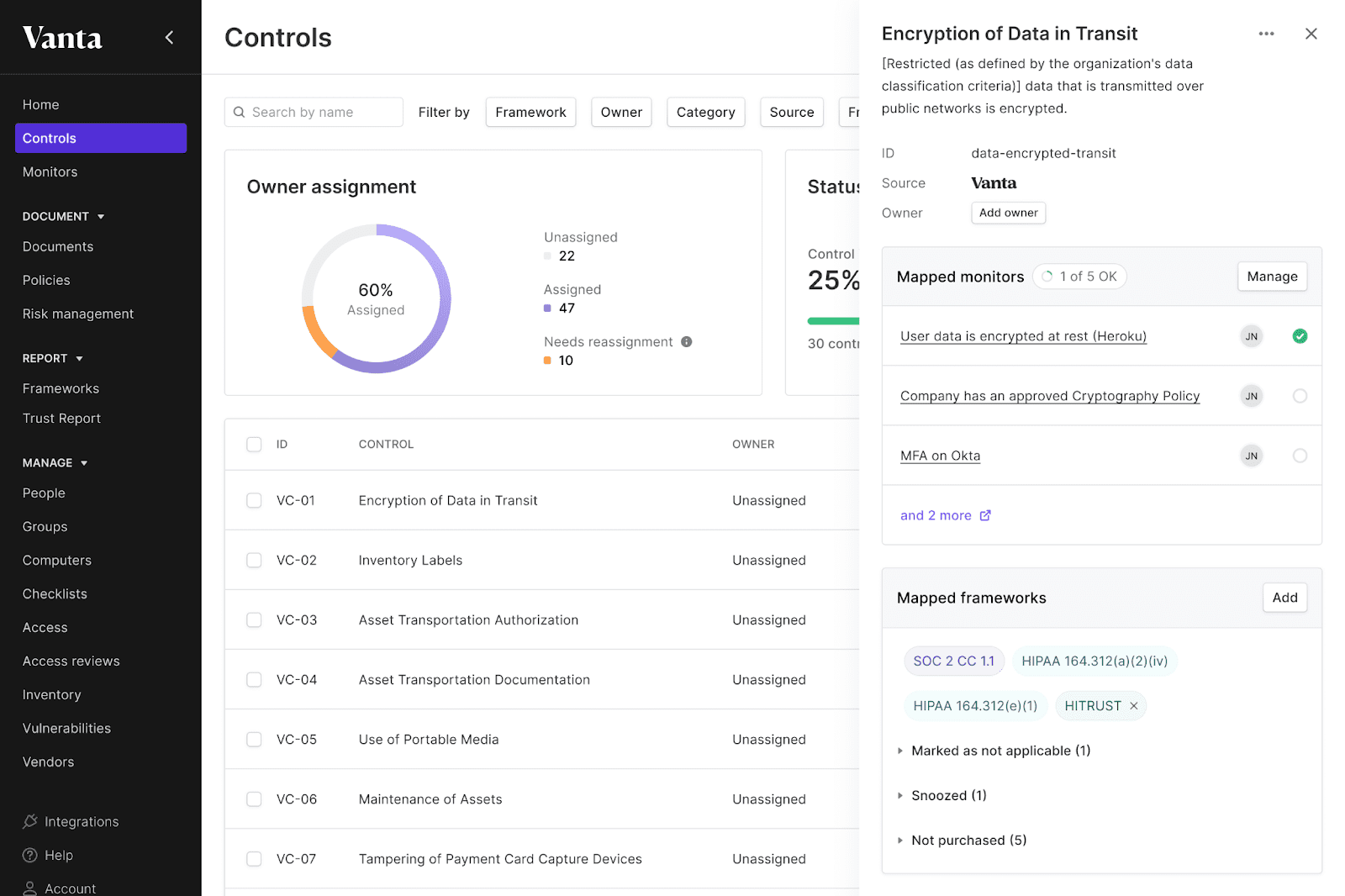
Vanta is best known for automating security and compliance frameworks like SOC 2 and ISO 27001.
Strengths:
- Easy compliance certification preparation
- Automated internal evidence collection
- Simple UI for security programs
Limitations
- Vendor risk management is not its primary focus
- Limited continuous monitoring across vendor ecosystems
- Vendor assessments are compliance-oriented rather than risk-intelligence driven
Vanta does great with internal compliance, but organizations needing advanced third-party risk management typically require a more specialized platform.
Learn more about Vanta and other TPRM competitors
Safe Security
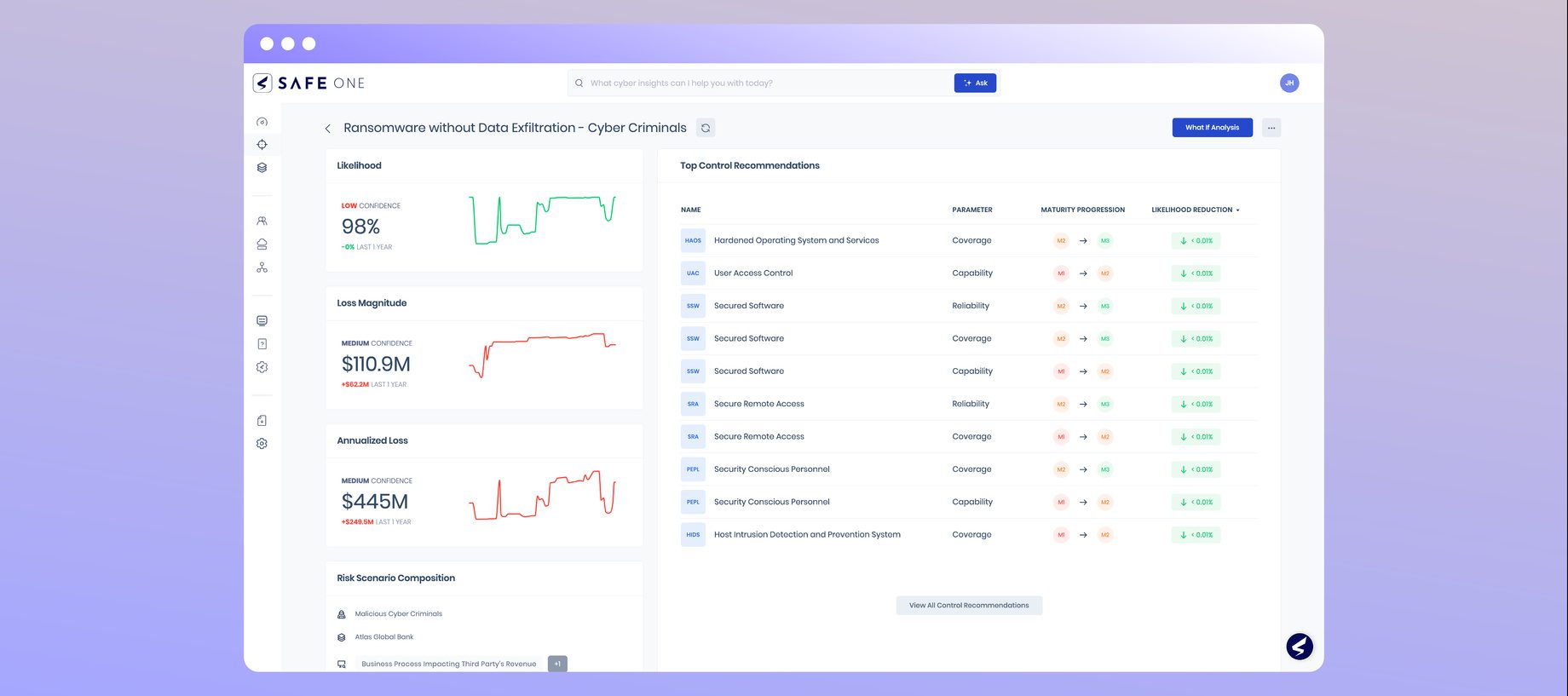
Safe Security focuses on risk quantification and ongoing vendor risk analytics.
Strengths:
- Continuous monitoring signals
- Risk quantification modeling
- Emphasis on measurable risk reduction
Limitations:
- May not provide end-to-end TPRM workflow automation
- Deep control validation still depends on vendor documentation processes
- Safe Security is valuable for organizations prioritizing risk scoring models and executive reporting
Safe Security platform comparision
Cyber GRX
CyberGRX pioneered a shared assessment exchange to reduce questionnaire fatigue.
Strengths
- Reduced duplication across vendors based on common data sets
Limitations
- Point-in-time risk assessment model
- Limited real-time vendor intelligence
- Not designed as a fully AI-powered vendor risk management platform
See how Cyber GRX stacks up against alternative TPRM solutions
Comparison chart: VISO TRUST vs Whistic, UpGuard, Vanta, and Safe Security
Compare leading vendor risk management platforms across assessment workflows,
continuous monitoring, and TPRM maturity.
Legend: ● Yes ○ Partial ◌ No
| Capability | Recommended:VISO TRUST | Whistic | UpGuard | Vanta | Safe Security |
|---|---|---|---|---|---|
| AI powered vendor assessments | Yes | Partial | Partial | Partial | Partial |
| Security questionnaire management | Yes | Yes | Yes | Yes | Partial |
| Continuous monitoring of vendor security posture | Yes | Partial | Yes | Partial | Yes |
| Real time vendor alerts | Yes | No | Yes | No | Yes |
| Evidence-based risk scores | Yes | Partial | Yes | Partial | Yes |
| ISO 27001 support | Yes | Partial | Partial | Yes | Partial |
| End-to-end TPRM workflow | Yes | Partial | Partial | No | Partial |
| Scales for teams managing vendors based on criticality | Yes | Partial | Partial | No | Partial |
How to Choose the Right Whistic Alternative
If you’re a security leader evaluating a vendor risk management platform, this decision isn’t about replacing a questionnaire tool.
It’s about answering a more strategic question:
Does this platform materially reduce third-party security risk or just organize it?
When evaluating a risk management platform, ask these critical questions:
1. Are risk assessments automated or manual?
Most vendor risk programs break at scale because they rely on human review of documentation.
If your team is manually reviewing SOC 2 reports, ISO 27001 certifications, penetration test summaries, and policy documents, you have two structural problems:
- Review depth varies by analyst
- Throughput is capped by headcount
That means risk assessment becomes a capacity issue, not a control issue.
An AI-powered risk management platform should:
- Review vendor documentation automatically
- Map controls to your security frameworks
- Identify gaps and inconsistencies
- Produce defensible, evidence-backed risk scores
If risk analysis still depends on how much time an analyst has this week, your program will not scale, and your risk exposure will outpace your review velocity.
For a CISO, the real question is: Does this platform reduce dependency on manual interpretation while increasing assessment consistency and audit defensibility?
2. Is monitoring continuous or just a snapshot in time?
A vendor passing a security questionnaire in Q1 does not mean they’re secure in Q3.
Threat actors do not operate on annual reassessment cycles.
Point-in-time assessments create a false sense of control. What matters is:
- Continuous monitoring of vendor security posture
- Real-time detection of material changes
- Updated risk scores as exposure evolves
A modern third-party risk management platform should surface:
- Changes in attack surface
- Newly disclosed vulnerabilities
- Material compliance lapses
- Emerging concentration risk across your vendor ecosystem
If your risk visibility pauses between annual reviews, you’re managing paperwork, not risk.
For CISOs, the standard should be: Would I know within days, not months, if a critical vendor’s risk profile changed?
3. Do you have real-time vendor visibility?
Security questionnaires tell you what a vendor says about themselves.
Real-time vendor intelligence tells you what is actually happening. There’s a material difference.
An enterprise-grade vendor risk management platform should:
- Correlate internal vendor documentation with external signals
- Detect degradation in security posture
- Alert your team automatically
Trigger reassessment workflows when risk thresholds are crossed
If your team only revisits vendors when contracts renew, you lack operational control over third-party risk.
For a CISO reporting to the board, the question becomes: Can I confidently state that we have real-time vendor visibility across our critical suppliers?
If the answer is no, the tooling isn’t mature enough.
4. Does the TPRM platform scale as vendor counts grow?
Vendor ecosystems expand faster than security teams.
New SaaS providers. New regional vendors. New regulatory requirements.
If your TPRM workflow requires proportional hiring as vendor counts grow, the operating model is broken.
Scalable vendor risk management requires:
- Automated assessment workflows
- Policy-driven risk tiering
- Vendors based on risk criticality receive differentiated review depth
- Automated reassessment triggers
- AI-powered documentation analysis
The platform should allow you to manage 500 vendors with the same team that previously managed 150.
If growth requires hiring analysts simply to process questionnaires, the model is not sustainable.
For a CISO balancing budget and risk exposure: Does this platform compress operational overhead or expand it?
5. Does it support both security risk and compliance teams?
Security and compliance are not the same function, but they are operationally intertwined.
Security cares about actual exposure.
Compliance cares about defensibility and documentation.
A mature platform must support both.
Security teams need:
- Evidence-based risk scores
- Visibility into vendor security posture
- Continuous monitoring
- Prioritized remediation
Compliance teams need:
- Audit-ready reports
- Traceable assessment workflows
- Documentation aligned to frameworks like ISO 27001
- Demonstrable oversight processes
If your risk management platform forces you to choose between operational security intelligence and compliance documentation, it will create internal friction.
For CISOs, the right question is: Does this platform strengthen both risk reduction and regulatory defensibility, or does it primarily solve one?
Organizing Risk vs Reducing Risk
Many Whistic competitors, including UpGuard, Vanta, Safe Security, CyberGRX, and Black Kite, solve important parts of the vendor risk challenge:
- Questionnaire exchange
- External risk scoring
- Compliance automation
- Risk quantification
- Security posture monitoring
But solving one component does not equal comprehensive third-party risk management.
It is to:
- Reduce the material third-party security risk
- Prevent supply chain exposure
- Ensure continuous oversight
- Provide defensible reporting to the board
- Scale without operational collapse
When evaluating a Whistic alternative, the core question isn’t: “Does it improve workflow?”
It’s: Does it materially change our risk posture, and can I defend that improvement to the board and regulators?
That is the standard an enterprise-grade vendor risk management platform must meet.