NIST CSF 2.0 Governance
Simplify NIST CSF 2.0 vendor risk management with automated evidence collection, outcome mapping, and continuous monitoring that keeps assurance fresh across your suppliers and third parties.
What is NIST CSF?
The NIST Cybersecurity Framework (CSF) is a voluntary, outcome-based framework designed to help organizations manage and reduce cybersecurity risk.
CSF 2.0 introduces a new Govern Function, alongside Identify, Protect, Detect, Respond, and Recover, and places stronger emphasis on supply chain oversight. It also uses Profiles and Tiers to describe current and target cybersecurity outcomes and track progress over time.
CSF 2.0 defines outcomes rather than prescriptive controls. In practice, teams map their internal controls to those outcomes for reporting.
Common control areas
Asset and risk management, access control, data security, vulnerability management, monitoring, incident response, recovery, and supply chain risk
Typical artifacts
Policies and standards, risk registers, inventories, diagrams, pen test reports, incident response plans, vendor/subprocessor lists, contracts, and NIST CSF assessment spreadsheets
NIST CSF 2.0 requirements for third-party risk
12.8.1
Establish a supply chain risk program
Define objectives, policies, roles, and risk tolerances for vendor oversight. Integrate with enterprise risk management to align with business priorities.
12.8.2/12.9
Use contracts to enforce requirements
Include reporting obligations, breach notification, audit rights, and subprocessor disclosures. Maintain a current vendor and supplier inventory.
12.8.3
Perform due diligence before onboarding
Conduct NIST CSF-aligned assessments for high-impact vendors. Collect evidence of coverage and evaluate residual risk and compensating practices.
12.8.4
Monitor suppliers throughout the relationship
Refresh evidence regularly, track remediation, and trigger reassessments after scope changes or incidents.
12.8.5
Plan and exercise incident response
Coordinate escalation paths, practice joint response, and align communications with critical suppliers.
12.8.5
Handle offboarding cleanly
Revoke access, ensure data return or destruction, and close obligations at offboarding.
Challenges in manual CSF 2.0 assessment
Evidence scattered across emails and spreadsheets
Manual tracking makes it difficult to maintain a comprehensive view of vendor compliance documentation and status.
Outdated questionnaires and inconsistent scoring
Legacy assessments lead to inconsistent scoring, unclear risk levels, and unreliable vendor evaluations.
Slow follow-ups and unclear ownership
Manual outreach creates delays and makes it challenging to know who is responsible for driving each step forward.
Limited visibility into vendor subprocessors
Fragmented data makes it hard to see which subprocessors vendors rely on – and how those relationships impact overall risk.
Stale assurance between reviews
Point-in-time reviews leave long gaps with no visibility, making continuous vendor monitoring nearly impossible.
Difficulty comparing vendors without a shared structure
Inconsistent formats force teams to piece together information manually, preventing clear comparisons across vendors.
How VISO TRUST streamlines NIST CSF vendor validation
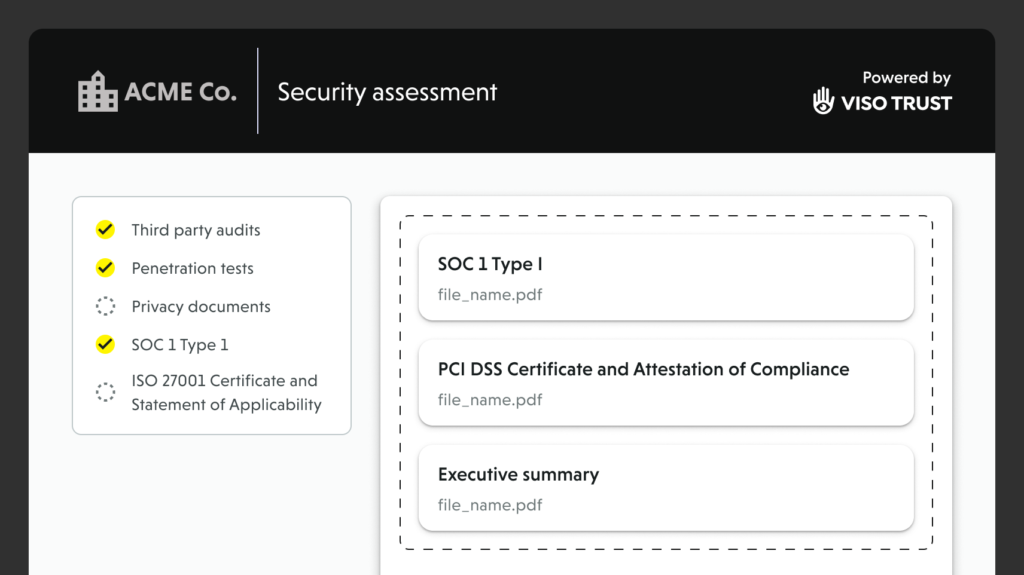
Automated artifact collection
Our AI Agent requests exactly what’s needed—policies, test results, procedures, risk registers, subprocessor lists – follows up automatically, and organizes submissions by outcome.
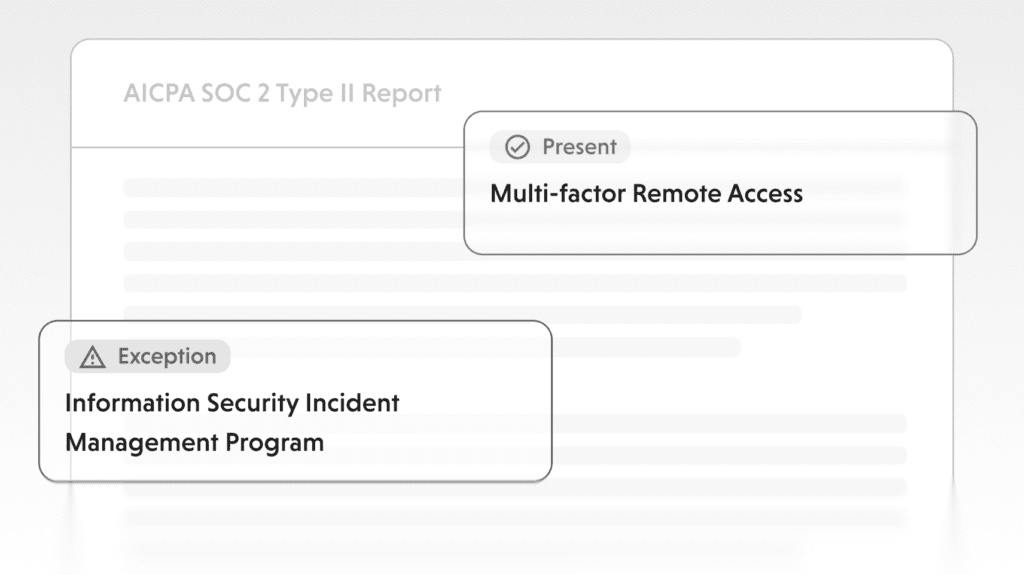
Evidence validation and outcome mapping
Artifacts are linked to CSF Functions, Categories, and Subcategories. Signals are scored with rationale, gaps, and remediation guidance, fully traceable back to the source.

Continuous assurance
Monitoring flags expirations, incidents, and supplier changes. Re-checks refresh vendor posture without waiting for yearly cycles.
Frequently asked questions
Build confidence across your vendor ecosystem.
Start simplifying NIST CSF 2.0 compliance with VISO TRUST today.