HIPAA compliance for third-party vendors
Take the hassle out of HIPAA vendor compliance with automated evidence collection, easy validation, and continuous checks that keep assurance fresh.
What is HIPAA?
HIPAA is a U.S. law that protects the privacy and security of protected health information (PHI). It applies to covered entities (providers, health plans, clearinghouses) and their business associates and subprocessors who handle PHI.
- Security Rule: Defines administrative, physical, and technical safeguards.
- Privacy Rule: Governs how PHI can be used and disclosed
Because many organizations rely on vendors for critical services and controls, vendor due diligence and ongoing assurance are essential for HIPAA compliance.
Common control domains: risk management, access control, transmission security, audit logging and monitoring, incident response, workforce security, contingency planning.
Common control areas
Risk management, access control, transmission security, audit logging, incident response, workforce security, contingency planning
Typical artifacts
BAAs, risk analyses, encryption and access policies, network/data flow diagrams, pen test reports, audit logs, SOC reports, subprocessor inventories, incident response playbooks
HIPAA requirements for third-party risk
12.8.1
Set vendor security standards
Define minimum safeguards for vendors that handle PHI, aligned to HIPAA requirements and data flow scope
12.8.2/12.9
Due diligence before onboarding
Perform HIPAA risk assessments. Collect and evaluate artifacts that demonstrate control effectiveness
12.8.3
Business Associate Agreements (BAAs)
Execute BAAs that codify HIPAA obligations: data handling, breach notification timelines, right to audit, and subprocessor approvals
12.8.4
Access control and data protection
Require least privilege, MFA, encryption in transit/at rest, logging, and access monitoring. Validate joiner/mover/leaver processes
12.8.5
Ongoing monitoring
Refresh evidence regularly, track remediation, and adapt to service or scope changes
12.8.5
Incident management
Require tested incident response, clear escalation paths, and time-bound PHI breach notifications
12.8.5
Audit-ready compliance
Maintain a traceable, evidence-backed audit trail with owners, findings, and closure notes linked to HIPAA requirements
Challenges in manual PCI DSS assessments
Evidence scattered across email, tickets, and spreadsheets
Information lives in disconnected tools, making it hard to maintain a complete and reliable view of vendor documentation.
Outdated questionnaires that miss current controls and scope changes
Static questionnaires fail to reflect evolving controls or new risks, leaving assessment gaps and outdated assurance.
Slow follow-ups and unclear owners for missing or expired items
Manual reminders create delays and confusion, with no clear accountability for resolving expired or incomplete evidence.
Inconsistent scoring and interpretations
Subjective interpretations lead to inconsistent scoring, making vendor comparisons unreliable and difficult to standardize.
Limited visibility into subprocessors and fourth-party dependencies
Opaque vendor ecosystems make it challenging to understand downstream dependencies — and the risks they introduce.
Assurance that goes stale between annual reviews
Point-in-time assessments leave long periods with no visibility into changes, weakening continuous oversight and compliance confidence.
How VISO TRUST streamlines PCI vendor validation
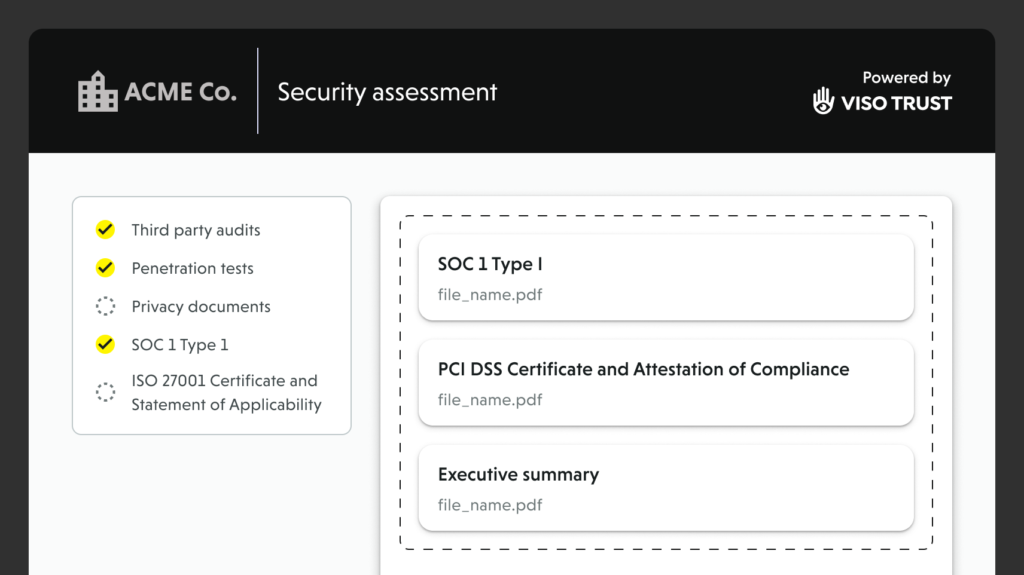
Automated artifact collection
Our AI Agent requests only the HIPAA-relevant documents (BAAs, policies, test reports, SOC reports, subprocessor lists, etc.) and vendor-focused HIPAA compliance checklist. And handles outreach and follow-ups, and organizes submissions by requirement.
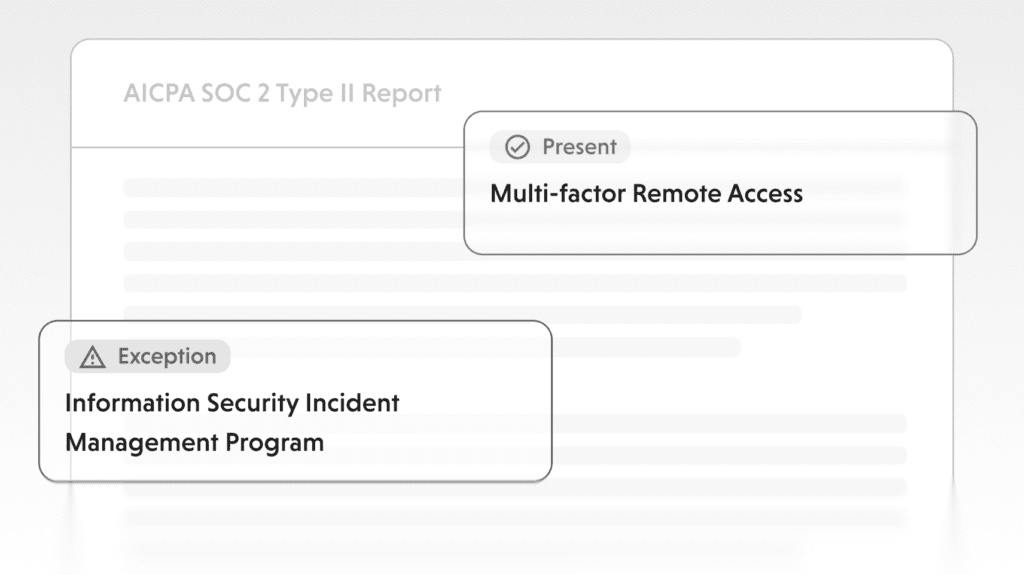
Evidence validation and control mapping
Artifacts are parsed, linked to HIPAA safeguards, and scored with rationale, gaps, and remediation guidance – fully traceable back to source evidence. Supports both ongoing HIPAA risk assessments and one-time checklist reviews.

Continuous assurance
Monitoring detects expirations, incidents, or subprocessor changes. Triggered re-checks refresh vendor posture, so assurance never goes stale. This keeps third-party HIPAA compliance current even as vendors and their subprocessor networks change.
Frequently asked questions
Stop chasing evidence. Start proving compliance.
Talk to us about automating your HIPAA vendor assurance.