ISO 27001 risk assessment
Simplify ISO/IEC 27001:2022 vendor assessments with automated evidence collection, ISMS mapping, and continuous monitoring that keeps third-party assurance fresh across your portfolio.
ISO/IEC 27001 is the international standard for building and running an information security management system (ISMS). The standard takes a risk-based approach: define scope, assess risks, treat them, and keep improving through audits and reviews.
Many organizations pursue certification, but certification isn’t required to apply ISO 27001 practices. In practice, ISO 27001 connects risk management, policies, and controls to business objectives – forming the foundation for ongoing compliance.
What’s new in 2022?
ISO/IEC 27001:2022 aligns Annex A with ISO/IEC 27002:2022, consolidating 93 controls into four themes: organizational, people, physical, and technological. Supplier and ICT supply chain topics are now explicitly covered in controls A.5.19–A.5.22, with cloud service use called out in A.5.23.
Common ISMS areas
Risk management, access control, cryptography, logging and monitoring, incident response, business continuity, supplier security, and cloud security.
Typical artifacts
ISMS scope, risk register, treatment plan, Statement of Applicability (SoA), policies and standards, inventories, pen test reports, incident response plans, contracts, SLAs, and audit summaries.
ISO 27001 requirements for third‑party risk
12.8.1
Set vendor security requirements
Define minimum expectations for any vendor touching your data or systems, aligned to ISMS scope and services.
12.8.2/12.9
Perform due diligence before onboarding
Run ISO 27001 risk assessments for critical vendors. Collect artifacts that prove control effectiveness and evaluate residual risk.
12.8.3
Use contracts to enforce security
Include obligations for incident notification, reporting, right to assess, data handling, and subprocessor disclosure.
12.8.4
Protect access and data
Require least-privilege access, MFA, encryption, monitoring, and proper joiner-mover-leaver processes.
12.8.5
Monitor and manage changes
Refresh evidence on a cadence, track remediation, and trigger reassessments after material changes or incidents.
12.8.5
Plan and test incident response
Run joint exercises with key suppliers, define escalation paths, and coordinate communications.
12.8.5
Keep audit‑ready record
Trace evidence back to source artifacts (SoA, policies, contracts) for internal reviews and external ISO 27001 audits.
Challenges in manual ISO 27001 assessments
Evidence scattered across emails and spreadsheets
Documentation lives in multiple places, making it difficult to maintain a unified and trustworthy view of vendor compliance.
Outdated questionnaires and inconsistent scoring
Legacy assessments and subjective scoring create gaps in accuracy, consistency, and confidence in vendor risk evaluations.
Slow follow-ups and unclear ownership
Manual reminders cause delays and confusion, with no clear responsibility for completing missing or overdue items.
Limited visibility into vendor subprocessors
Fragmented information makes it hard to identify vendor subprocessors and understand the downstream risks they introduce.
Assurance that goes stale between annual cycles
Point-in-time reviews leave long visibility gaps, reducing confidence in continuous compliance and vendor oversight.
Hard to compare vendors without a shared structure
Inconsistent documentation and formats force teams to interpret data manually, making vendor comparisons slow and unreliable.
How VISO TRUST streamlines ISO 27001 vendor validation
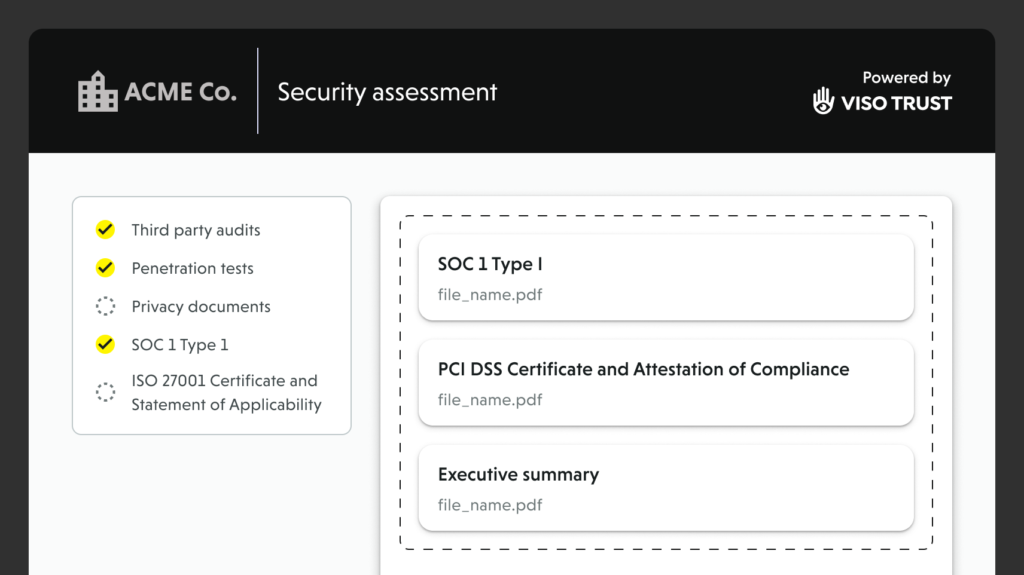
Automated artifact collection
Our AI Agent requests exactly what’s needed – ISMS scope, SoA, risk register, policies, test results, incident procedures, audit reports, and supplier disclosures. It follows up automatically and organizes submissions by requirement.
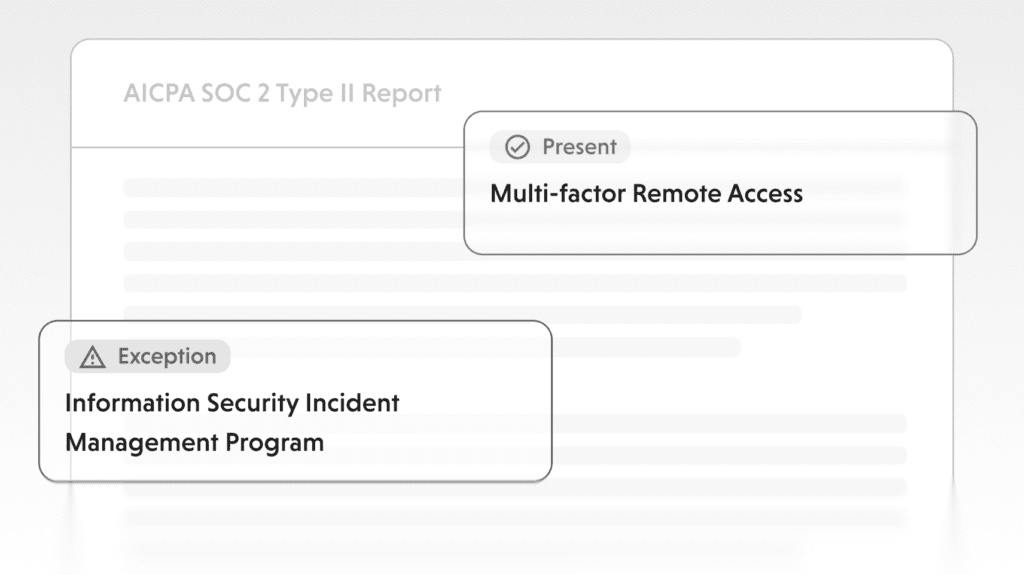
Evidence validation and mapping
Artifacts are parsed and linked to ISO 27001 requirements and Annex A themes. Signals are scored with rationale, gaps, and remediation guidance. Everything remains traceable back to the source.
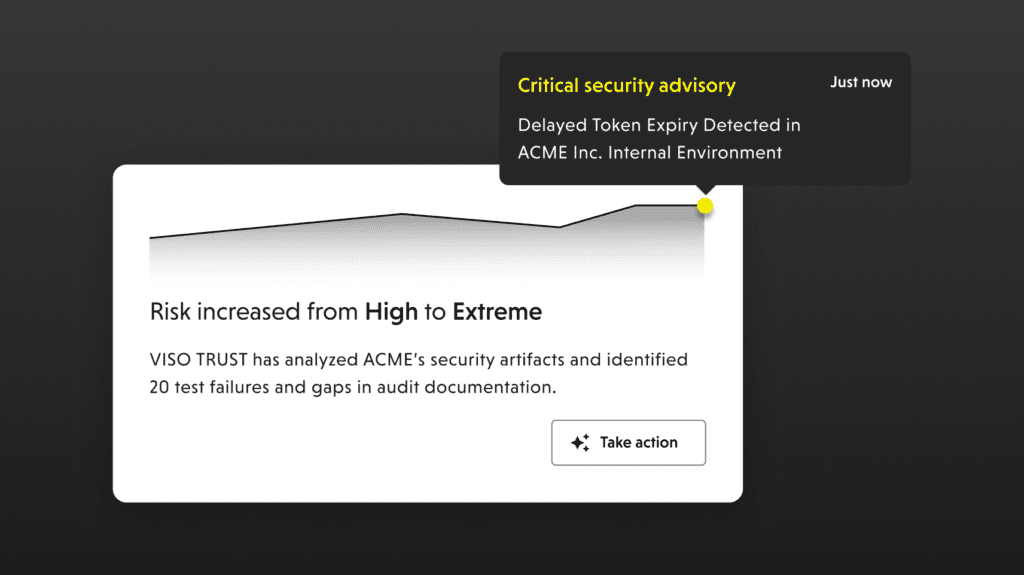
Continuous assurance
Monitoring flags expirations, incidents, and supplier changes. Triggered re-checks refresh posture between audit cycles, keeping third-party risk visible year-round.
Frequently asked questions
Stop chasing spreadsheets. Start proving ISO 27001 compliance.
Talk to us about automating your vendor risk assessments.
