Take control of your third party security posture
Third party risk is undermining your security and crushing your team. VISO Trust solves this problem.
Third party risk is undermining your security and crushing your team. VISO Trust solves this problem.
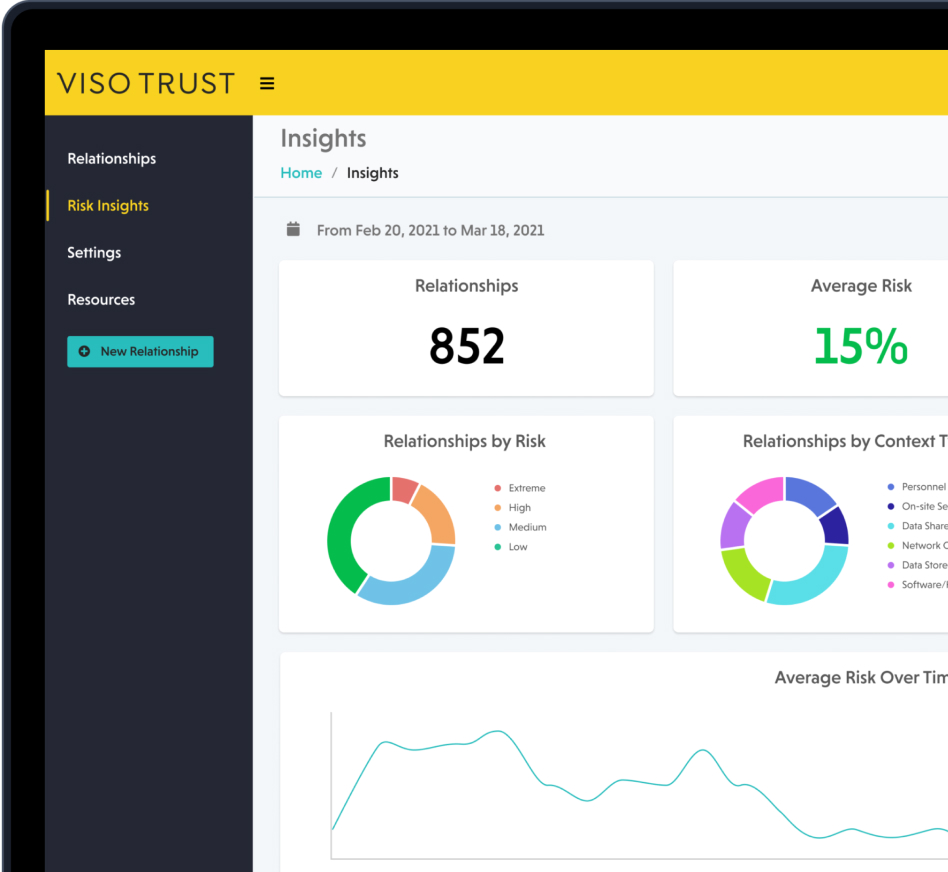
VISO Trust is the only SaaS third party cyber risk management platform that delivers the rapid security intelligence needed for modern companies to make critical risk decisions early in the procurement process.
Turnkey Due Diligence simplifies an otherwise complex process and allows companies to effortlessly assess third parties.
By using curated AI to extract relevant insights from artefacts, Document Intelligence determines the security posture of vendors automatically, without any user interaction.
Using intelligent automated workflows and notifications, Lifecycle Automation engages vendors at key intervals to keep risk insights up-to-date and accurate.

↑100%
<2min
↓90%
↑117%

Meet the PanelMeet the PanelMeet the Panel Meet the PanelMeet the PanelMeet the Panel Meet the PanelMeet the PanelMeet the Panel Meet the Panel

Job title, Company

Job title, Company
This is the third post in a three part series on creating a reusable ML pipeline that is initiated with a single config file and five user-defined functions. The pipeline is finetuning-based for the purposes of classification, runs on distributed GPUs on AWS Sagemaker and uses Huggingface Transformers, Accelerate, Datasets & Evaluate, PyTorch, wandb and more.
This post will cover the training and testing (inference) steps. These are the core steps in a ML pipeline where a model is hyper-parameter tuned and the test set is used to measure performance. If you have landed on this post first, check out the first post in the series detailing the pipeline setup and the second post detailing the data steps.
Training and Tuning
The reason I have combined Training and Tuning into one section is that Tuning just is a set of training jobs where performance is incrementally improved through the changing of hyperparameters. As such, underneath the covers, the two types of jobs are calling the same code. Like we have previously, let’s take a look first at perform_training() and perform_tuning() to see how the code interacts with Sagemaker.
Consectetur senectus sed nunc ut risus. Morbi vitae felis eu non viverra ultricies. Lobortis egestas maecenas et nam viverra. Arcu gravida imperdiet vitae ut sed. Aliquet sem varius ornare enim turpis metus sed ante. Curabitur porta amet quam suspendisse sem sollicitudin tortor faucibus.
Sit eget sed tempus id et vitae. Aliquam mattis sed varius in nulla urna cras amet amet. Faucibus quis fermentum volutpat odio pellentesque habitant commodo nunc porttitor.

VISO TRUST is taking a fundamentally different approach from existing third-party risk management solutions. So, here's a few quick tips and questions that we wanted to cover with you. Anything else on your mind? Reach out to us and share your feedback!
In addition to Third party attested documents such as SOC reports, ISO 27001 certifications and Statement of Applicability, penetration testing reports, etc. vendors can upload self attested documents such as completed questionnaires, security policies etc. These will carry a lower level of assurance in our model. If none of these are available, we do provide a streamlined questionnaire that is specific to the controls that are in scope that can be answered by the vendor via our vendor portal.
We have thousands of vendors across many customers in our system. However, while we take advantage of the network effect this provides, we are not an exchange. Our automated assessments are specific to how you do business with the vendor.